
5 Expert Letterhead Design Tips To Draw Readers Into Content
Letterhead designs are one of the first chances a business has to make a good impression. A single letterhead design can tell customers a lot about your brand image and the company in general. That is why, despite common notion, designing letterhead is actually a difficult graphic design task, even for the best graphic designers. As a business owner, this can be daunting. But, don’t worry! As long as you use the letterhead design tips in this post to help you

Must Know Web Publishing Terms To Start A Career In Development
Web publishing, or online publishing, is exactly what it sounds like. It is the process of creating and publishing content on the internet. More broadly, it refers to the process of creating and uploading websites entirely, updating pages or even just posting a blog. If you are looking to break into the field of digital publishing and get started as a web programmer, there are some important terms you will want to familiarize yourself with in order to learn all you

Why Virtual Machine Software For Windows 10 Is Worth It
If you are a tech junkie, you have probably heard about virtual machines. But, did you know that virtual machine software for Windows 10 makes this trending technology available to average tech users, like yourself? Probably not. You probably assumed that only HPUX users could benefit from virtualization. Find out why you should consider using a virtual machine software to benefit from virtualization below. Exploring OS Options If you want to explore the many different operating system choices available, a virtual

5 Essential Strategies For A Successful Lab Design
Designing a lab is more than just designing an effective space. It is also about creating a conducive research environment using the available resources. For a lab to be effective, it needs to be flexible, efficient, and safe. These factors all increase the IT productivity of people working in the space. There are also specific challenges you have to face when creating a lab design. Things such as airflow and waste management must be integrated correctly for the research space to

Crucial SQL Server Activity Monitor Features To Identify Bottlenecks
If you are new to the SQL server environment, it can be a bit daunting trying to figure out all the features and tools on your own just as it would be to figure out how to mirror image Photoshop projects on your own. This is especially true if you are just entering into the field of server management for the first time. But, as long as you know the key features and tools provided by SQL servers, you will find

How To Deploy Continuous Delivery For Mobile Apps Production
Deploying code for any software takes time and testing. In large-scale systems or production environments, a continuous delivery system streamlines the code deployment. Compared to testing code before release, the process automates building and testing software faster. Interesting to app developers, continuous delivery for mobile apps allows quicker software releases. These are incremental releases that are much more easily managed by developers and users across mobile platforms. Below, we explore how to implement continuous delivery in apps. Plan The Continuous Delivery

How Online Writing Platforms Make An Excellent Essay For You
If you are still struggling to write a good essay void of grammar errors or plagiarism that is because you have not started using the right tools. Essay writing has become much easier with special online tools such as Copyscape, Grammarly and other plagiarism checking tools. So, before saying do my essay, it is important to find out how the essay writing service company you are hiring do their writing. This article talks about important online tools that are used in
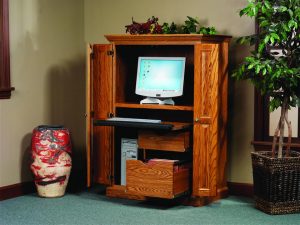
Must Have Computer Cabinet Features For A Productive Workspace
If you are shopping for a computer cabinet, you want to be sure that you are buying the absolute best cabinet within your price range. However, as with anything else you buy, you need to know what you are looking for. Remember to look for these features in any computer cabinets you consider while shopping. That way, you are sure to buy the best computer cabinet for your needs. Security If you plan to use your computer cabinet somewhere other than

Download A Wifi Analyzer Windows Software To Boost Mbps Speeds
Sometimes, there can be a major drop off from Ethernet internet connection to WiFi connections. Unlike a direct connection, WiFi connection operates on different channels. If your router is located in a crowded office building or apartment complex, interference on the channel could be slowing down your internet speed. In order to figure out the best channel for your router, individuals need to analyze WiFi connections. Quite simply, a WiFi analyzer windows software will troubleshoot many wireless internet related problems. Luckily,

Tips For Building (And Using) Android Apps Securely
While some tech extremists predict the imminent end of software as we know it now that voice-controlled artificial intelligence can control our devices, it hardly seems that mobile apps are disappearing. In fact, every year another 200,000 or so apps become available in the Google Play Store, and Apple’s App Store should offer more than 5 million apps by 2020. Becoming familiar with app-building processes is a smart way for smartphone users and tech enthusiasts to gain more experience and comfort

Useful Passive RFID Tags Features For Business Applications
For business owners, RFID tags have a ton of potential applications, unlike your old SSD drive. After all, RFIDs provide the means for allowing virtually any object use in business operations at all to be identified by computer systems. But, in order to take start implementing the use of RFID tags at your business, you should first know their features and benefits. Find out the passive RFID tags features and benefits every business owner need to consider below. No Battery Unlike

How A CDN Can Prevent Critical Damage For Website Administrators
If you are a website administrator, you have probably heard about CDNs. A CDN, or content delivery network, can greatly benefit every website in a multitude of ways. Yours is no exception. Find out why you should consider using a content delivery network below. Global Reach CDNs give your website global reach. Global reach would not otherwise be impossible. But, it certainly would not be as enjoyable for your page visitors. It would also be a lot more expensive to do

The Advantages Commercial ETLs Have Over Writing Your Own SQL
ETL tools have come a long way since their creation. Whereas custom SQL tools had the advantage in the early days because of their versatility and flexibility, ETLs have become far more sophisticated in recent years. Now, ETL tools have surpassed manual SQL in a lot of ways, making them an attractive option for many who need an effective database solution. While using a commercial ETL tool like Domo won’t be the correct choice for every use case (there will always

Unknown Citizen Journalists That Revolutionized News Media Reporting
Citizen journalism occurs when the public plays an active role in the gathering and reporting news. This could be anything from recording video on an iPhone to sending out a

How Modern Cancer Research Findings May Lead To A Cure For Cancer
New technologies are developing daily, each designed with a specific purpose and audience. In medical research, advancing technologies have been designed to detect cancer cells in blood. In this post,

Best Apps For Pharmacists To Have Concise Database At Your Fingertips
Pharmacy companies are constantly coming out with new, innovative ways to provide healthcare to the community. As technology continues to expand, more and more opportunities are coming to the app

7 Reformatting Computer Preparation Steps To Take To Protect Data
Reformatting is the process of completely erasing everything from the hard drive of your computer and then reinstalling the essentials – like your operating system, applications, and personal files. It’s

Straight Talk Walmart Phones Make Unlimited Data Affordable
Walmart is known for selling a variety of products at the lowest price. Their phones and electronics are no exception. Walmart phones offer a wide selection from disposable phones for

How To Access Google Timeline To Edit Saved Location Tracking Entries
Last year, Google Maps introduced a timeline map. This feature allows users to revisit their travels from any given day. In this post, Internet users can learn five exciting features

Prime95 Download Sources To Test Overclocked CPU Stability For Free
Prime95 is software designed to stress test personal computers to ensure stability. The free software was designed by George Woltman to find new mersenne prime numbers. It is frequently used

Most Exciting Google X Moonshot Factory Innovations Not Yet Released
Google X, now referred to as X, is Google’s semi-secret facility in California. The research and development company aims to, according to the website, “invent and launch ‘moonshot’ technologies that

Best Mini Camera Choices For WiFi Connected HDR Surveillance Images
A smartphone may not always be the best option for recording video, depending on the situation. When it comes to Facebook rules, you can post almost anything shot on your

New Abbey Roads Studio Audio Technology Offers Mastering Services
Arguably the most famous recording studio in the world, it is difficult not to think about The Beatles when mentioning Abbeys Road Studios in London, U.K. Some of the world’s

How Google Mail Account Domains Differ In Countries Around The Globe
Gmail users in the United States know it is Google’s email service, but hardly anyone refers to it as Google Mail. This opposite may be the case if you reside

Important Protections Antispyware Solutions Offer PC Users
SUPERAntiSpyware is a free software that offers a range of protection to computer users from viruses, adware, worms and spyware (among others). Still, most average computer users don’t think of

How Backdoors Offer Perfect Hacking Strategies For Encrypted Devices
Backdoors are methods by which a technology user can gain unauthorized access to a program or computer function outside of normal security parameters and proper IPtables confirguation. While the average
