
How Streaming Content Works Using A VPN
A VPN (Virtual Private Network) is a method used to securely connect to a server, encrypting your data so that it can’t be intercepted. It’s primarily used by businesses to give employees access to their resources while they are remotely located. It also has many other benefits, especially for streaming enthusiasts. For one thing, VPNs allow you greater access to geographically restricted content on American Netflix and BBC iPlayer, for example. Keep reading to learn why streaming content uses a VPN

How To Get Started With Deep Learning As A Service Frameworks
There are several steps to get started with deep learning as a service frameworks. With AI and ML taking over the tech industry, innovative companies are increasingly turning to revolutionary deep learning as a service solutions (DLaaS). These advanced solutions enable computers to learn independently, with little supervision from humans. Of course, DLaaS offers remarkable advantages for fast-paced, tech-savvy industries around the globe. After all, it completely alters how our brains function, learn, and process information. As a tech enthusiast yourself,

5 Features The Best SVOD Platforms Have To Offer
There are several features the best SVOD platforms have to offer. Today, the video streaming industry is worth over $5 billion. Undoubtedly, TV viewers are turning to subscription video on demand (SVOD) instead of cable TV. Indeed, many users switch to these platforms to avoid costly cable bills and pay-per-view services. Simultaneously, they only pay for the content they want. As an app user, you should familiarize yourself with the different features SVOD platforms have to offer. This way, you can

How Event Management Works For Today’s Tech Companies
The first step to successfully managing an event is through planning. There should be a written schedule for the event that lists all activities and preparations required. It is essential to use some of the best planning techniques to ensure the event’s success. A good schedule should contain precise details on what needs to be done before, during, and after the event. Event management entails strictly prioritizing events and adhering to schedules without any delays or deviation from set objectives. Event

5 Core Features From Cloud Email Spam Blocker Apps
There are several core features of cloud email spam blocker apps. These advanced applications protect inboxes from unwanted, unauthorized and fraudulent email messages 24/7. With advanced, AI-powered capabilities, these powerful tools successfully block millions of spam emails everyday. As a tech enthusiast, you’ll want to use a cloud-based email spam detector to keep annoying spam messages out of your inbox. Read on to learn the core features from cloud email spam blocker apps. Claim Filing First off, cloud email spam blocker

5 Types Of Security Scans Every Organization Should Perform
There are several types of security scans every organization should perform. With day-by-day cyber threats against digital assets increasing, organizations need to use scanners for powerful security protection. These security scanners inspect networks to detect, diagnose, and prevent security flaws. As a cyber security specialist, you’ll want to know about the different types of scans that today’s tech companies are conducting. This way, you deter online hackers from gaining access to your valuable systems. Here are the top types of security

The Best Apps And Tools For Digital Marketing In 2022
Digital marketing is the thing that brings your revenue to its full potential. With everything going on online, digital marketing is one of the best ways to reach a potential customer. This is because the internet has become the main medium for information. That’s why we’re going to discuss the benefits of digital marketing and the perfect digital marketing toolkit for successful growth. The tools and apps we’re going to mention largely rely on the people using them. Digital Marketing Vs.

5 Types Of Infrared Conversion Filters For Photographers
There are several types of infrared conversion filters for photographers. Notably, photographers can convert their cameras to capture photographs in infrared light. With these modifications, the cameras typically block out visible light. Then, photographers can add a filter so the infrared light can easily pass through the sensor. As a photographer, you need to know the different types of infrared conversion filters. This way, you know which lighting best suits your different options. Plus, you can capture more captivating photos. Read

How To Track Competitor Twitter Followers Over Time With Analytics
There are several steps to track competitor Twitter followers over time with analytics. With over 300 million users, Twitter is currently one of the largest social networks in the world. This means brands across the globe need to conduct competitor analysis and devise marketing strategies for promoting on this platform. As a social media marketing manager, you should get familiar with monitoring and tracking competitor followers on Twitter, as well as other high-traffic social sites. This way, you can assure that

How Do Pneumatic Valves Work For Industrial Businesses?
Anyone who has any familiarity with valves has likely heard of pneumatic valves. In fact, these gadgets are even regularly used by individuals in the top IT career paths. A little about these types of valves for those not in the know: These are valve assemblies that use compressed air to operate. When you increase the amount of air pressure, the result is a decrease in fluid flow through the valve. This article will go over how pneumatic valves work, why

How To Create A Social Media Schedule Calendar To Post Content
There are several steps to create a social media schedule calendar to post content. With these calendars, marketers can plan out and schedule their social media website posts ahead of time. In addition, they can plan their posts for the week, month, or even the year if they have content ready. Of course, this makes their jobs easier, reduces stress, and increases productivity since their posts can automatically upload. As a social media marketer, you should know how to create a

5 Best Email Segmentation Tools For Your Business
There are various best email segmentation tools for your business. Segmentation assists companies in dividing subscribers into small groups based on characteristics. Companies can create endless audience types with updated segments as contact lists grow. As a result, businesses can deliver more direct and targeted emails. As a business owner, you can segment emails by interests, engagement, behavior or location. Read on to discover the best email segmentation tools for your business. Automation Tools First, automation tools are reliable for business

How to Empower Customers to Tell Your Company’s Story
What’s better than your customers telling your story for you? Your customers effective digital advertising and talking about your company is the best thing that can happen to your business. When we talk about advertising, it is always considered a one-on-one strategy. The company and customers are on the opposite sides of the table, and it is hard to believe when a company says that their product is the best. However, if a friend or a colleague talks about a
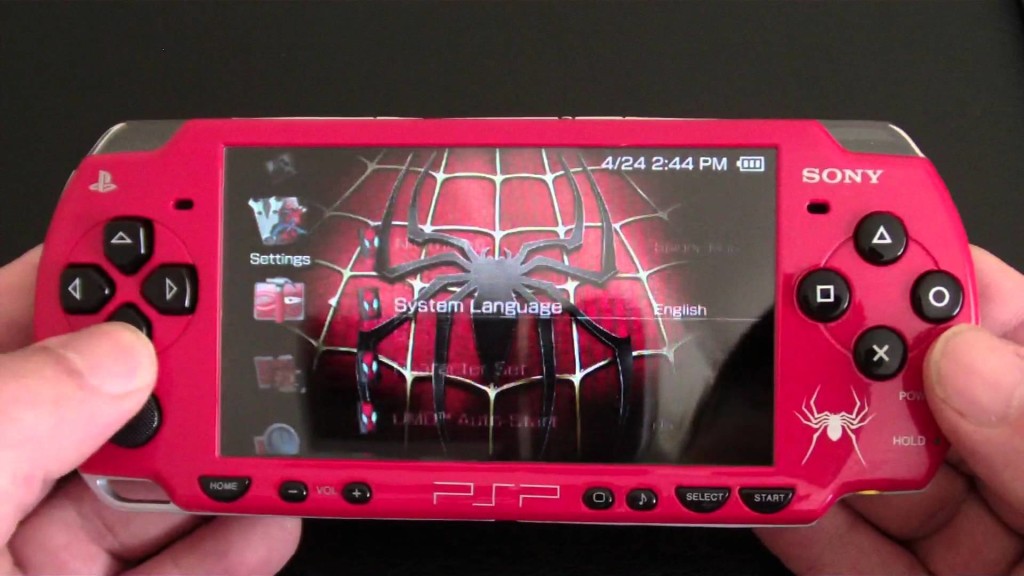
Why The Sony PSP 2000 Gaming Console Was A Technology Market Flop
The psp2000 was released in 2007 as a successor to the original PSP launched by Sony in 2004 (Japan) and 2005 (rest of the world). It was Sony’s answer to

How Android Froyo Update Still Powers Millions Of Phones
Google Android came out with the “Froyo” update in May 2010. Froyo was Android 2.2, while the latest update is at 6.0. In this post, technology users can see what

Website Stickiness Practices To Keep Web Visitors On Your Site Longer
A website’s stickiness is anything that encourages visitors to stay longer. If a website is “sticky,” users will stay on the site for an extended period of time and return

7 Ways The iFax App Improves Outdated Faxing Technologies
Faxing is often considered an outdated practice along with witch-burning and butter-churning. However, the reality is that fax machines still exist and people still have to use them. Whether you’re

Rejection Phone Numbers To Let Someone Down Without Confrontation
Dealing with creeps at the bar or strangers pestering you for a date is worse than slow internet. A rejection phone number is a fake number that can be given

Why Interstitial Ads Are Quickly Dominating Mobile Marketing Strategies
Interstitial ads are advertisements that cover the entire screen of their host application. Unlike banners or pop-ups, interstitial ads can require a user’s full attention for a certain length of

Chatterbots AI Technology Mimics Human Behavior For Practical Uses
Chatterbots are computer programs that converse via text or audio, mimicking a human conversational partner. Unlike talking with humans and wondering DidTheyReadIt, these chat bots are waiting to respond instantly.

5 Questions To Ask To Effectively Choose Web Developer Services
A web developer is a pivotal person for any online business. This is the person who will design the entire site. Therefore, it is very important that you are able

Examples Of Geolocation Software Uses To Prevent IP Address Fraud
Geolocation is the real life location of an object, identified by radar or internet connection. The term is also used in process of determining this location. Many modern devices include

Kirby Reviews Suck But Best Vacuum Cleans Up Better Than Competition
Kirby is an American manufacturer of vacuum cleaners based in Ohio. The company has been in business for over 100 years, and exclusively sells its product via authorized distributors through

LinkScanner Antivirus Software Protects PCs From Malicious Websites
Desktop PC and laptop users have many options when it comes to internet security. Many people have anti-virus installed but sometimes a virus is discovered when it is too late,

5 Common Types Of Cybercrime To Protect Sensitive Data From Now
Crime that involves a computer and a network is defined as cybercrime. Interpol breaks down cybercrime into two categories. The first is advanced cybercrime, which includes, “sophisticated attacks against computer

Revolutionary Telepresence Technology For Improved Web Conferences
Telepresence is defined as the use of virtual reality technologies to make someone feel as if they are present elsewhere. More specifically, they give the appearance that the user is
