
Abstraction Definition For Encapsulation in Object Oriented Programming
The term “abstraction” has various meanings in general conversation. These definitions can be used to describe art and philosophy, among other things. Similarly, the abstraction definition is used in computer science. In the technology field, the abstraction definition is used to describe a central principle of object-oriented programming. It is easy to choose web developer employees to create a website, but it is not nearly as easy to learn object-oriented programming. However, if you have a passion for the job, before

New Chase Payment Method Simplifies Online Shopping Checkout
Chase Payment, better known as Chase Pay, is the bank’s latest attempt at staying competitive in the ever-evolving e-commerce market. Chase Pay allows user’s a safe and easy way to pay for goods at various online retailers. Perhaps you have seen a Chase Pay logo on your favorite online retailer’s site. Or perhaps you have been prompted to try out the new Chase payment method via email. Whatever the case, Chase payment has you intrigued. This post will explain the basics
InstallWatch Pro Alternatives To Track Registry And File Changes Simply
Cyber security is more important than ever these days. That is why it is important that you keep a close eye on your computer’s activity when trying to install MAMP or similar programs. There are several applications available to help you do just that. Installwatch Pro is one of many registry and file change detectors that can be downloaded straight to your computer. If you want an application that can help you track the activity on your computer, read below for

How VCE Vblocks Systems Help Simplify Business Virtualization
VCE is a coalition formed by international tech companies VMware, Cisco and EMC. Together, they are dedicated to the advancement and promotion of cloud computing and virtualized environments. VBlocks are some of their latest projects. They are a converged infrastructure designed to help companies make the switch to virtualization. If you are a business owner interested in firewall management and employing virtualization in your company, you may want to consider the benefits of VCE’s innovation. Versatile VBlocks are self-contained data center
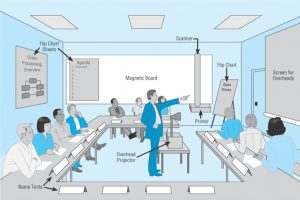
Prepare A JAD Session To Bring Key Players Together To Collaborate
JAD stands for Joint Application Design. JAD sessions involve a series of meetings and workshops. During these sessions, key players for a project will discuss the needs of their client or project and develop solutions for them. If you are a business leader at an ebusiness or a regular corporation, you may find that a JAD session could be helpful. These sessions bring together the leaders of a large project, allowing them to brainstorm together. If you want to learn more

Wintel Partnership History Of Intel And Window’s Tech Market Domination
Wintel is a nickname given to any computer running a Windows operating system on an Intel microprocessor. The early aughts were the golden years for companies like Teraflop and Wintel, but what is going on with the two companies now? As a tech enthusiast, you may be interested to hear the history of the partnership. This post will cover the basics of the rise and fall of Wintel and its market domination. What Is Wintel? As simply stated above, Wintel is

MCSE Certification Checklist Of Testing Requirements And Procedures
A Microsoft Certified Solutions Expert, or MCSE, certification affirms your expertise in computer infrastructures running on Microsoft Servers. They are a great addition to an IT professional’s resume because they serve as an expansion of one’s skill set. This is especially true if you already have a SNIA certification on top of it. If you would like to obtain your MCSE certification, you need to be aware of the specific procedures and requirements for doing so. There are work experience requirements,

Complete Outlook.pst Guide To Manage Microsoft Email Account Data
In computing, a .pst file stands for personal storage table. Outlook, a personal information manager from Microsoft, utilizes Outlook.pst file often. However, many Microsoft users do not know about or understand the use of Outlook.pst files. If you are a Microsoft user interested in learning more about Outlook.pst files that contain business data or personal data, continue reading below for the information you need. What Is An Outlook.pst File? An Outlook.pst file is a type of Outlook Data File that is

Rooted Phones Guide For Android Users To Understand Rooting Process
If you are an Android user, you may have heard the term “rooting” before. This type of rooting does not have anything to do with trees. Instead, it involves altering your phone’s distros system. A rooted Android can do many things that a regular one cannot. If you are interested in learning about what a rooted Android is and how you can use it, check out the basic information below. What Is A Rooted Android? A rooted Android is a device

Lenovo Accutype Keyboards Offer More Comfortable Typing Experience
Lenovo is the multinational technology company that developed the AccuType keyboard. Lenovo claims that the AccuType keyboard features a modern look and feel in addition to flatter keys that concave slightly. This is a new approach to keyboards like SwiftKey. These keyboards have been a topic of discussion for many Lenovo customers. Whether they love it or hate it, people have plenty to say about it. If you are interested in hearing more about the pros and cons of the AccuType

SNIA Certification Test Prep Resources To Help You Achieve Credentials
SNIA stands for Storage Networking Industry Association. The SNIA is a vendor-neutral network of professionals who are dedicated to advancing storage and information technology, not to be confused with SSL certification. If you work in the IT field, SNIA offers certification tests to reflect your knowledge of the field. There are many benefits to achieving SNIA certification. Some of these include employability, peer recognition and enhanced income potential. If you would like to receive these benefits and more from a SNIA
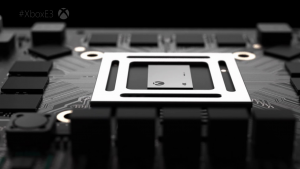
Role Teraflop Specs Play In Gaming Console Computing Performance
If you are an avid gamer, you may have come across the term teraflop from time to time. Recently, the term has gotten more attention due to a series of questions regarding the power it provides to gaming consoles like the Xbox One, PlayStation 4 and other upcoming projects from Microsoft and Sony. If you want to purchase the most powerful gaming console on the market, you may want to take teraflop specs into consideration. Below are some simple definitions and

Top 5 Momentus Apps That Demonstrate Creative, Innovative Design
Momentus Software is a software development company that marries technology and design. Momentus Software offers a variety of services to businesses including hardware integration, product design and app development. If your business is looking to ditch the freelance PHP beginners and work with a creative, innovative company on big projects, Momentus Software may be the right choice. Below are some of their most successful apps, so that you can see the talent and expertise they could bring to your project.

Top 5 Free Website Uptime History Monitoring Tools
If you own a website as a business, it is imperative that you know the website uptime history for your page. This is the figure that will impact traffic volume

How Do IT Experts Choose 4G Routers?
4G cellular connections are increasingly being used by businesses to connect their sites to the internet or to other sites on their Wide Area Network (WAN). Using 4G can be

Pros And Cons Of ColorWare Customization Services
ColorWare is a website that offers custom paint finishes to electronics that you love. When phone cases or laptop skins are just not enough, ColorWare lets you take the next

Top 5 Change Control Software For Smooth Migrations
Change control software is a necessary part of agile business, especially if you are just about to migrate to a new software, like Swiftstack. If you are an IT manager,

Essential Investments For Your Tech Business Infrastructure
When it comes to tech businesses, this category is no longer exclusively reserved for those who only work with all things IT. Other industries are finding it difficult to compete

Innovative Geofencing Technology Improves Operations Management
Geofencing is the latest technology trend impacting business and mainstream society alike. It is making almost as big a splash as outsourcing did a decade ago. However, it is still

When To Use VPN Services To Protect Your Browsing Data
The use of Virtual Private Networks is becoming increasingly more common as internet users, like you, become aware of the dangers of browsing without one. However, you may be wondering

Top Electronic Toys To Help Children Of All Ages Learn STEM Skills
Most parents think that kids should steer clear of electronic toys. However, this simply is not true. There are plenty of educational electronic toys that your child can greatly benefit

How White Label Solutions Make Customized Technology Affordable
White label solutions often offer small business owners a plethora of advantages over other brand name business software or even custom software development. However, many owners do not realize these

How To Measure Bandwidth To Avoid Internet Throttling Forever
Sometimes, internet service providers, or ISPs, will throttle your connection if you hit your allotted bandwidth data cap. This can be frustrating. However, it is also avoidable if you know

5 Mobile Apps That Can Be Used Significantly In Businesses
Before going into anything, here’s a clarification: This post is about mobile apps that are actually used as part of business operations. Presented here are not just mobile apps incidentally

Exciting Code Black Drone Features That Make It Easy To Fly
If you are a tech geek, you have no doubt wanted to buy a drone for quite some time now. These aerial gadgets are some of the most coveted of

How To Prevent A Denial-Of-Service Attack On Your Ebusiness
A denial-of-service attack, or DoS attack, is when a hacker prevents you from accessing services, particularly the internet. This is done by the unknown third-party attacker accessing either your computer
