
How To Build A DIY Inductor In 4 Simple Steps
If you enjoy tinkering with electronics, you may know what an inductor is. If not, you have come to the right place. An inductor is a passive electronic component that stores energy and resists changes in the electrical current that passes through it. The basic idea of inductors is very simple. You do not have to worry about trying to barter technology if you cannot afford a pre-fabricated inductor. If you are interested in learning how to make your own inductor

Important VMDK Basics To Get The Most Out Of Virtualization Solutions
VMDK stands for Virtual Machine Disk. VMware, a cloud and virtualization service, originally developed the VMDK file. Now, VMDK is an open file format. If you have never heard of a VMDK file before, you may also not know the basics of virtualization as a whole. In order to understand what a VMDK file is and how you can use it, continue reading below for an overview of virtualization basics. It is just like a 1950 Porsche – you should not
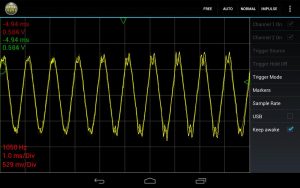
Complete Basic Oscilloscope Functions With These Top Apps
An oscilloscope is a device that is used to view oscillations, as of an electrical voltage or current, through a display on the screen of a waveform graph. The most common type of oscilloscope is seen in hospitals as a means of tracking a patient’s heart rate. However, an oscilloscope can be more than expensive medical equipment. Your very own phone can be used as one, just like the apps for pharmacists that are becoming popular. If you are interested in

Basic Representational State Transfer Guide For Use In Network Services
ReST stands for Representational State Transfer, an architectural style of communication primarily used in web applications and network services. In layman’s terms, it is a simple way of sending and receiving data between a client and a server. Many people may not know or understand the basic ideas behind Representational State Transfer in VMware Flings and other software. If you are interested in learning more about what ReST is and how it works, read below for an overview of the basics.

Nonrepudiation Guide To Understand Its Role In Email Security
What is nonrepudiation? If you use the internet to send and receive files and emails, you may want to find out, if you do not already know. It is an important part of keeping your computer, and ultimately your private information, safe. Nonrepudiation is a method by which your computer confirms the security of the files you send and receive in unified communications. It is frequently misunderstood by those who are new to IT security. This post will cover the basics

6 Best Elcomsoft Alternatives To Prevent A Corporate Security Breach
Elcomsoft is an IT security company headquartered in Moscow, Russia. IT security is a big concern for many business owners. Elcomsoft offers solutions to issues regarding password protection, system recovery and wireless security. Unfortunately, Elcomsoft caters to the needs of government and intelligence agencies. Although it is an excellent security system, Elcomsoft may not be the IT security answer for you. Thankfully, there are plenty of other services, like Mirapoint, that you can improve your computer’s security. See below for some
Programming Instantiation Guide To Data Modeling And Virtualization
Instantiation has many meanings in the world of technology. Largely to do with programming via Netbeans and similar, it is an important term for anyone interested in the field. If you want to learn more about the multiple meanings of this term, continue reading below. Object-Oriented Programming Object-Oriented Programming is centered upon the idea that programming should focus on the objects that the programmer wants to manipulate, rather than the logic behind how to do so. Instantiation in Object-Oriented Programming involves

4 Ways To Fix SYLK File Format For Unexpected Microsoft Excel Errors
A SYLK file is a Microsoft file format. SYLK stands for SYmbolic LinK. SYLK files are typically used to exchange data between applications, specifically spreadsheets. However, some Microsoft users tend to run into problems regarding SYLK files. If you use Microsoft and are familiar with VMDK basics, you may have seen an error message that says “SYLK: File format is not valid” when trying to open a text or CSV file. Unfortunately, there is no permanent solution to this error. However,
Popular MGCP Alternatives To Improve VoIP Protocol Data Encryption
MGCP stands for Media Gateway Control Protocol. It is a standard protocol utilized in Voice over IP (VoIP) communications. However, there are other VoIP protocols to choose from. Currently, there are four popular VoIP protocols available. To ensure that you choose the best VoIP protocol for you, we are going to provide a brief overview of several VoIP protocols like MGCP. If you are interested in learning more about the possibilities of MGCP and other VoIP gateway protocol options, continue reading

Overclocked CPU Guide For Beginners To Understand Associated Risks
Overclocking is the process of resetting a computer’s components in order to make it run faster than the manufacturer’s original speed. Oftentimes, it does not take any additional software or hardware to improve the performance of your computer. However, there are far more cons than pros to having an overclocked computer. If you are interested in learning about the disadvantages of an overclocked computer, read below for more. But first, you may want to gain a better idea of what overclocking

How To Install MAMP To Test Website Changes On A Local Apache Server
MAMP stands for Macintosh, Apache, MySQL and PHP. These are all features of the MAMP application that you can use for WordPress. Upon installing MAMP onto your Mac, you will have access to local PHP and MySQL servers. This means that the MAMP WordPress application can be used to test and develop your blog or website’s landing page design on these servers before going live. There are several benefits to the MAMP WordPress application. If you are interested in learning more

Innovative Overtime Fitness Technology Changes The Way You Workout
Overtime Fitness is a workout facility located in Mountainview, California. Because they are not a big-name gym, you may not have heard of Overtime Fitness. However, they played a big role in revolutionizing fitness and technology and will definitely be going viral soon. If you are interested in learning more about how Overtime Fitness changed the way people work out, see below for more info. Facility For Teens In 2006, Overtime Fitness opened its doors as the first fitness facility directed

Finding The Right DB 9 For Your PC Electrical Connections Project
A DB-9 connector is a type of D-subminiature connector. While these connectors will not help you with Swiftstack applications, a DB-9 was once used for a variety of purposes on PC’s. These connectors were often used to connect devices to the computer, such as keyboards, mice, and similar. There are still modern purposes for a DB-9 connector, however. If you are interested in learning more about this particular type of connector, let this post serve as a guide. What Is A

Using Customer Service AI Bots To Promote Customer Engagement
Customer service AI technologies have rapidly begun to impact modern businesses. As an IT administrator, utilize AI bots to promote customer engagement for your company. AI bots have greatly improved

The Best Way To Manage Multiple Social Media Accounts At Once
In today’s high-tech world, social media account management is crucial to any company’s success. Many IT managers struggle to run business social accounts effectively. Each platform requires various skills and

5 Best Homeschool App Types For Better Learning Experiences
Homeschool apps enable parents to teach their children more effectively. As a homeschooling parent yourself, you strive to give your kids the best education possible. In order to do that,

How To Use An App To Build Brand Awareness
Until recently, a well-designed website and a presence on social media was enough to satisfy most customer’s expectations. With an impressive number of Twitter mentions and Instagram followers, you could

5 Methods To Allow Remote Access To PC To Manage Your System
Remote access to PC allows users to maintain productivity throughout the day. As a tech enthusiast, remotely accessing your personal computers allows you to maintain your system without being physically present.

5 Essential Secure Home Video Monitoring System Requirements
Home video monitoring systems protect properties in the case of emergencies. As a tech enthusiast, consider developing a secure home video monitoring system to protect your home and belongings. Modern

A Guide To Finding And Removing Personal Information On The Internet
The internet holds many consumers’ personal information. As an avid internet user, you have searched your name on popular search engines like Google. The majority of users search their names

5 Innovative Chatbot For Lead Generation Strategies
Today’s industry leaders use chatbots for lead generation. They also improve customer experience for internet users and increase their sales as a result. Many marketing teams are even replacing their

How To Set Up Parental Control WiFi For Optimal Safety
As the internet continues to grow and more children start to use it on a daily basis, internet safety is becoming more crucial. Without parental control WiFi, parents struggle to

Why You Need A Security Orchestration Platform For Business
You know you need to secure your digital systems if you own your own business. However, how you secure those systems can vary widely. There are plenty of data security

5 Best Photo Online Storage Services For Safe Keeping
In today’s high-tech world, people constantly use their mobile devices to take pictures. They need the best photo online storage services to keep their memories safe. As an internet user,

How To Use AI For Small Business Industry Success
Technologies like artificial intelligence (AI) play a major role in any company’s success rate. More and more small business owners are implementing the latest technologies in an effort to improve

How To Improve Network Management And Enhance Security
With network administration, there is a focus on assets and resources, including switches, routers, and servers. It also involves updating software as needed. It includes the management and monitoring of
